Web Design Blog
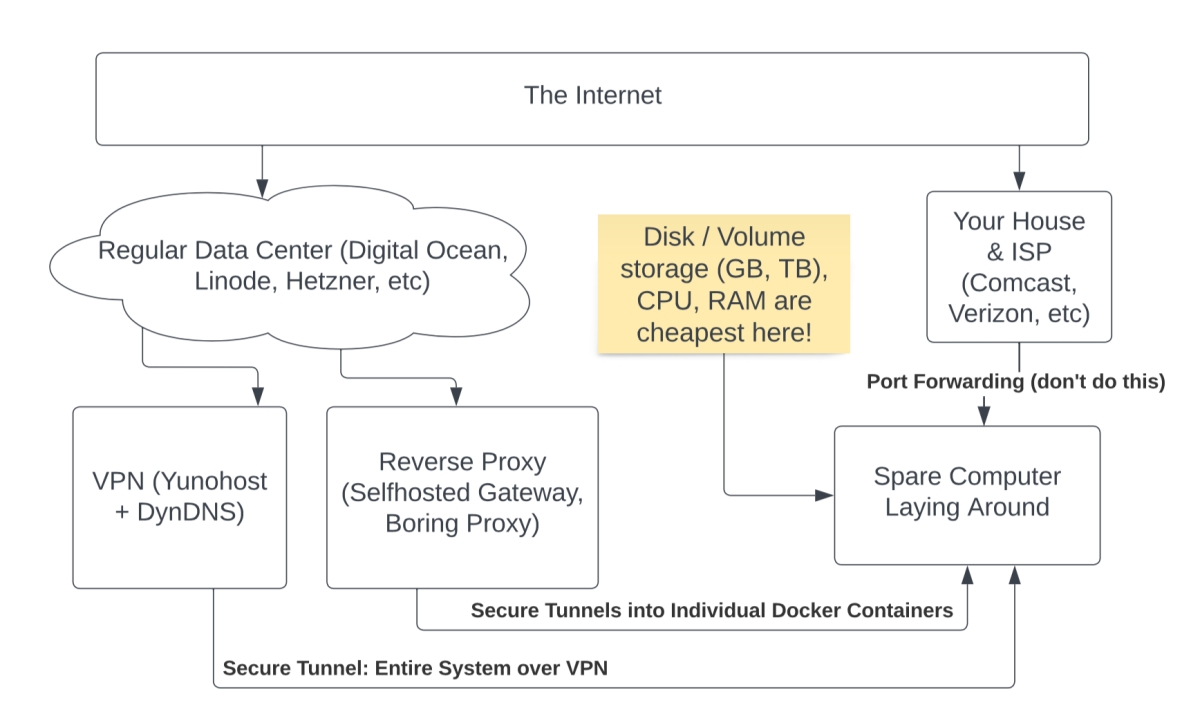
The following video discusses several common ways of self hosting apps and websites on your own hardware. This provides helpful cost saving information for business owners and non profits, which varies based on how much CPU and RAM are required vs. storage space (GB/TB). For users that require more than roughly 10gb of storage space, moving your VPS out of the cloud and using a reverse proxy to self-host your apps (on premises) is an easy way to save money, while keeping 100% control of your apps and data.
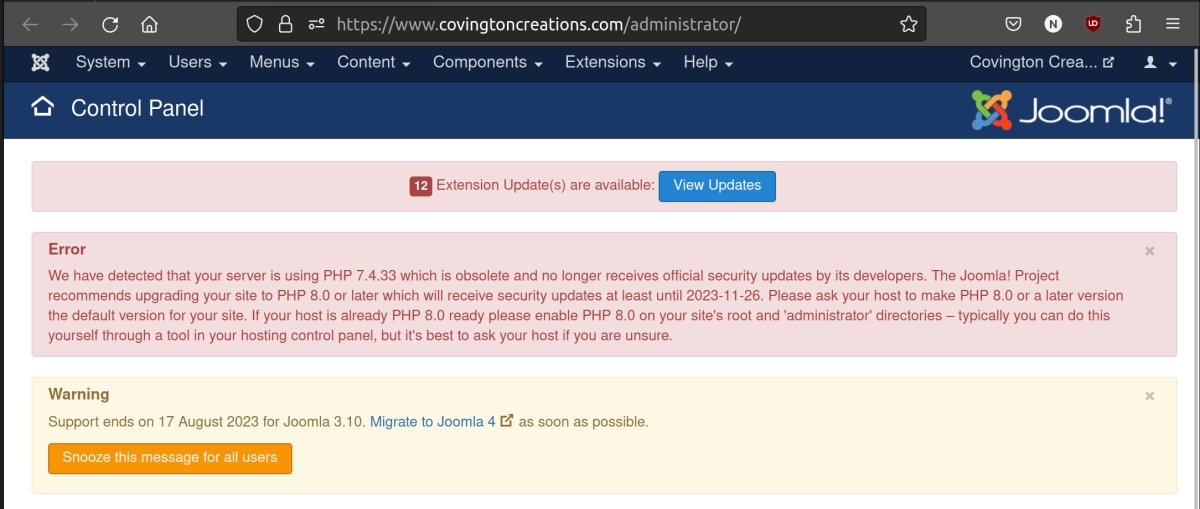
Does your Joomla site show this message in the /administrator dashboard?
Support ends on 17 August 2023 for Joomla 3.10. Migrate to Joomla 4 as soon as possible.
Did you know that AI can help enhance your website content, blog posts, google ads, and other marketing materials? Jasper is the AI Content Generator that helps you and your team break through creative blocks to create amazing, original content 10X faster.
This article contains some great examples of how to use AI to write content for your business. Since it's garbage in, garbage out, just like any other computer platform, it's important to deliver clear, concise prompts so that it actually delivers what you are looking for. Similar to putting the correct keyword into a Google search -
Learn how to use ChatGPT to level up your paid search efforts without sacrificing strategy, authenticity or creativity.
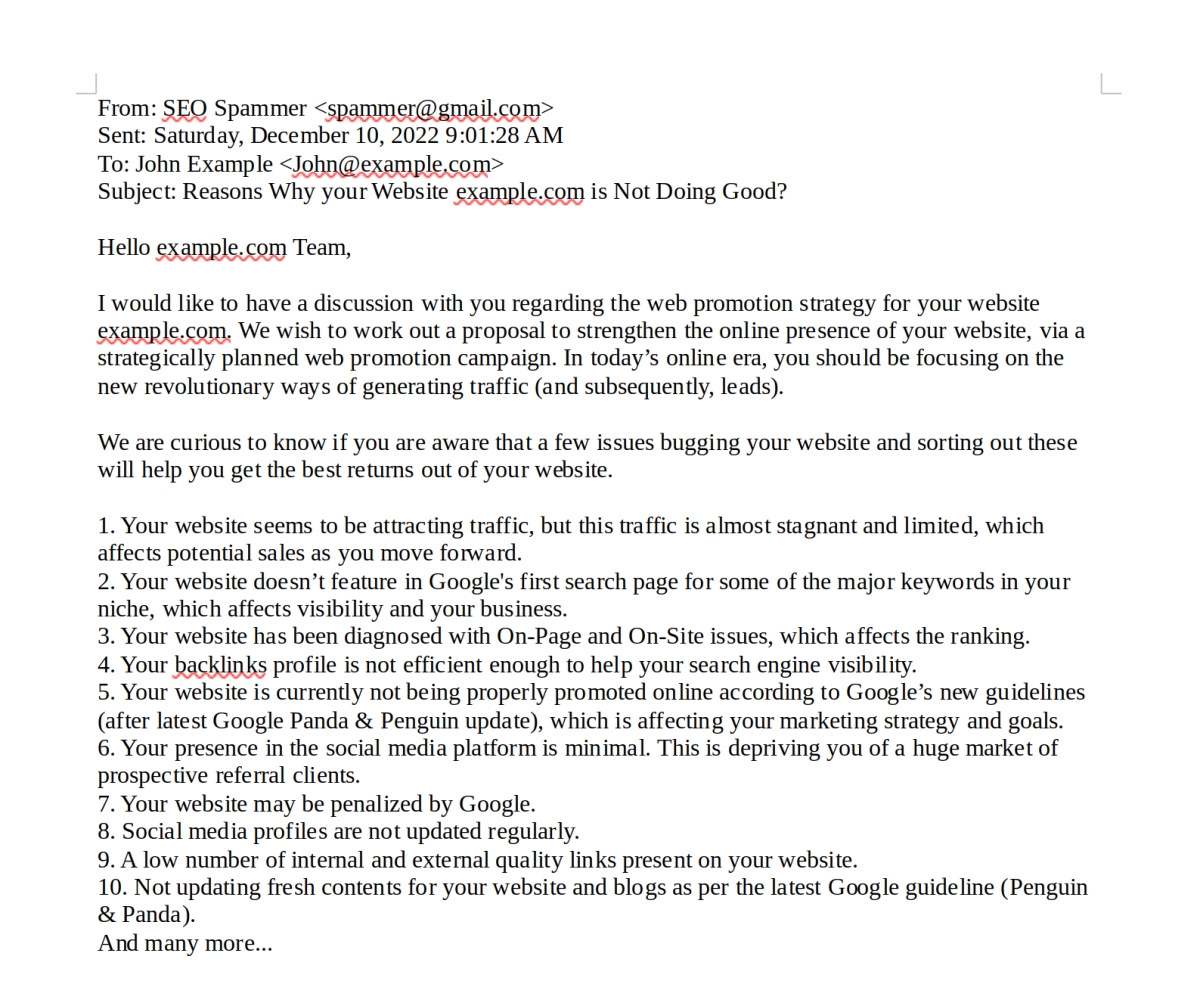
I'm posting this as a precaution to avoid these types of spam emails! If you're looking for someone to manage your website, or optimize it, we are available for hire.
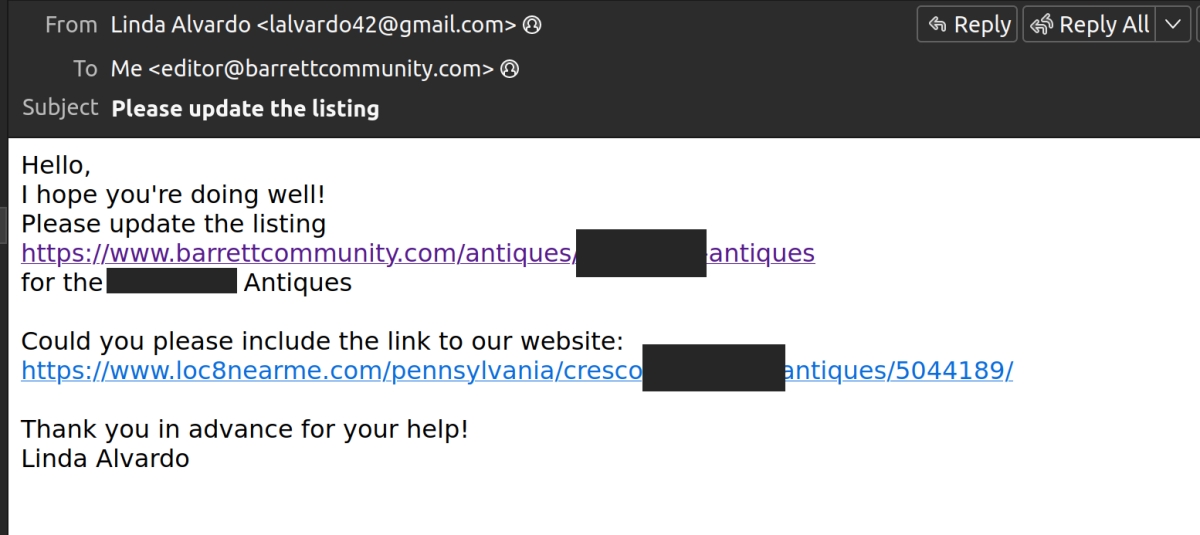
The SEO spammers are getting pretty advanced lately, below is an email that made it through the Office 365 spam filter a few days ago.
Frequently Asked:
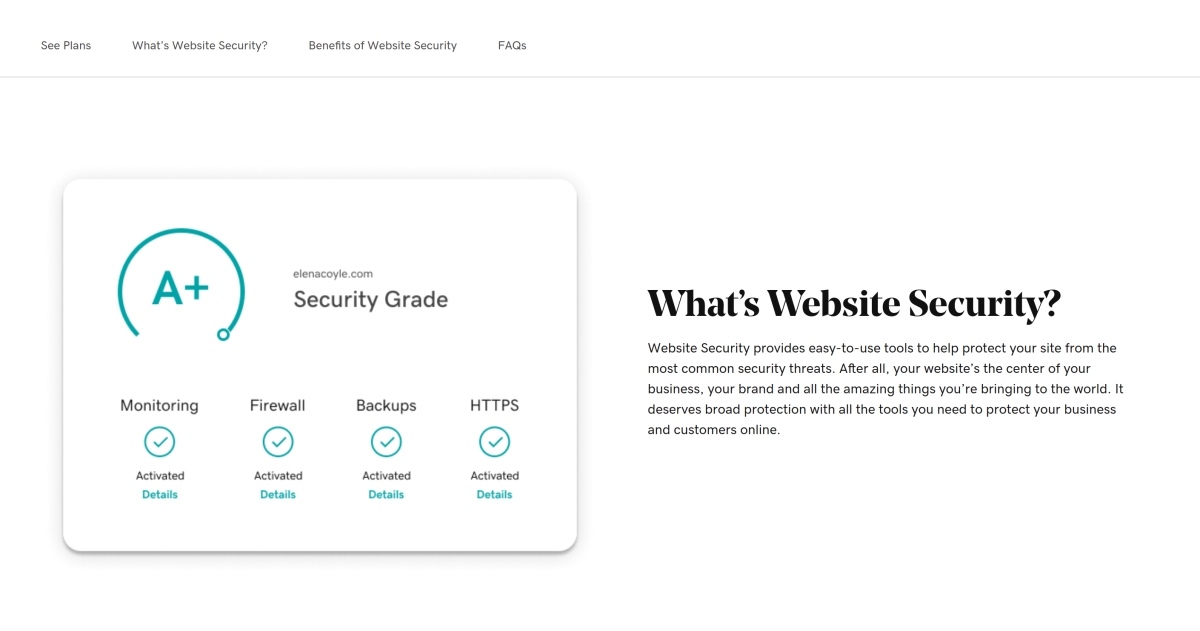
We were on the phone with godaddy this week for support, and the tech recommended we implement their website security/protection service (see below). Wanted to get your thoughts on this? What are the chances of someone injecting malicious code into our site, and or redirecting url's, etc? And-perhaps you already have some sort of protection in place?
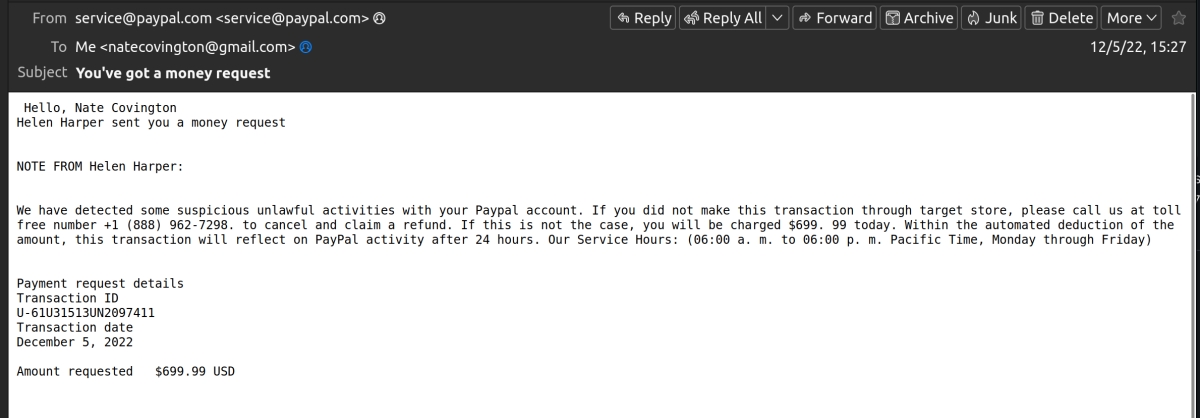
I received this message through my PayPal account and almost fell for it, figured I'd share and warn others.
Below is the full message they sent - their strategy is to use the "money request" feature in PayPal to trick you into calling a fraudulant 888 toll free number so they can try to gain access to your PayPal account.
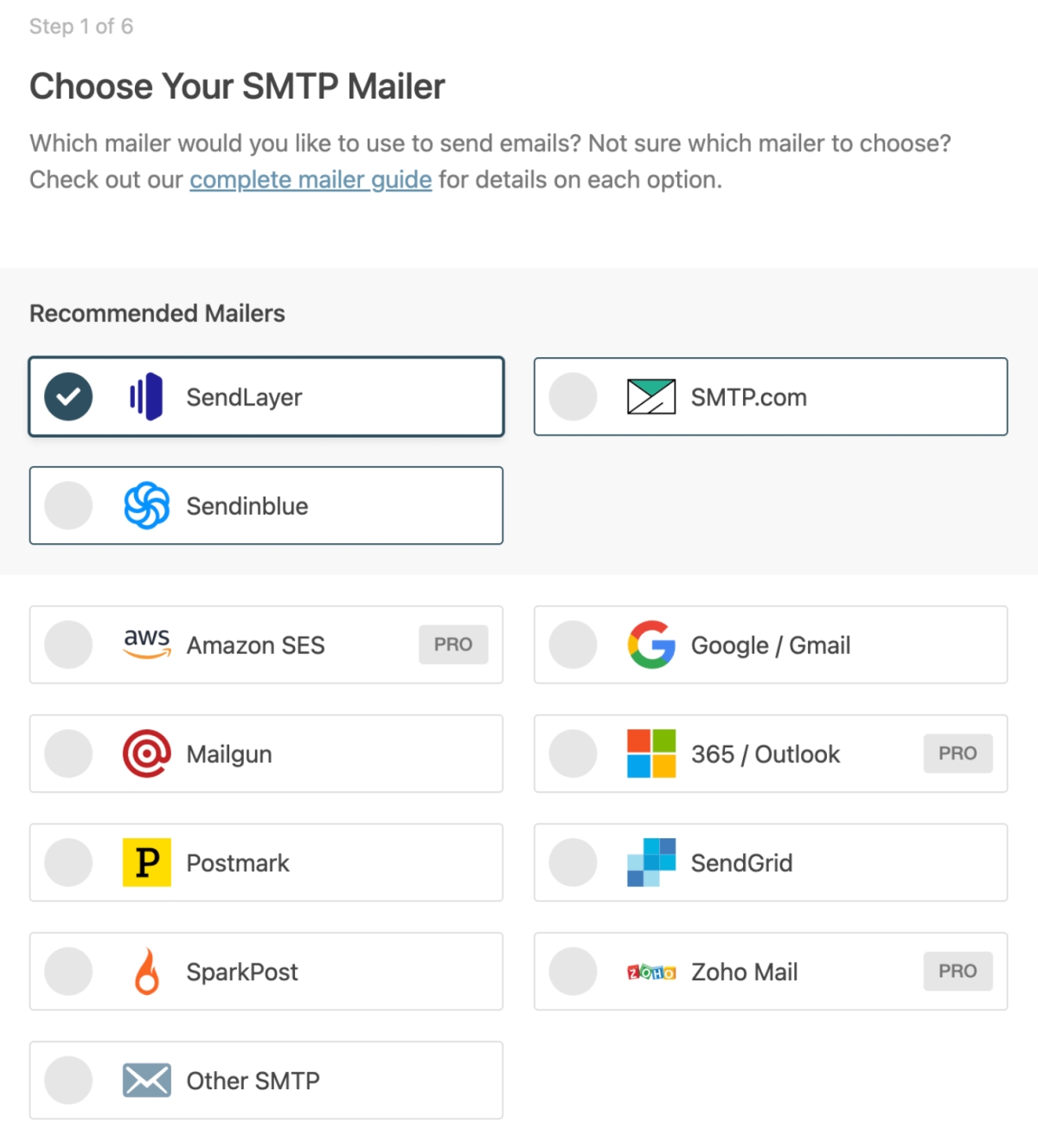
When comparing transactional email providers, it's important to confirm whether or not the plan includes "activity history" so you can use that provider's dashboard to see each individual e-mail that your website sent. This lets you determine if that lost password email, or the contact form notification email, was delivered properly.
Having problems with receiving email from your website? You most likely have a misconfigured web server.
I recently received this scammy email from Linda Alvardo regarding loc8nearme.com and wanted to share some findings. This is a "link building" attempt where they are asking me to change a local business listing where they found a missing website address.
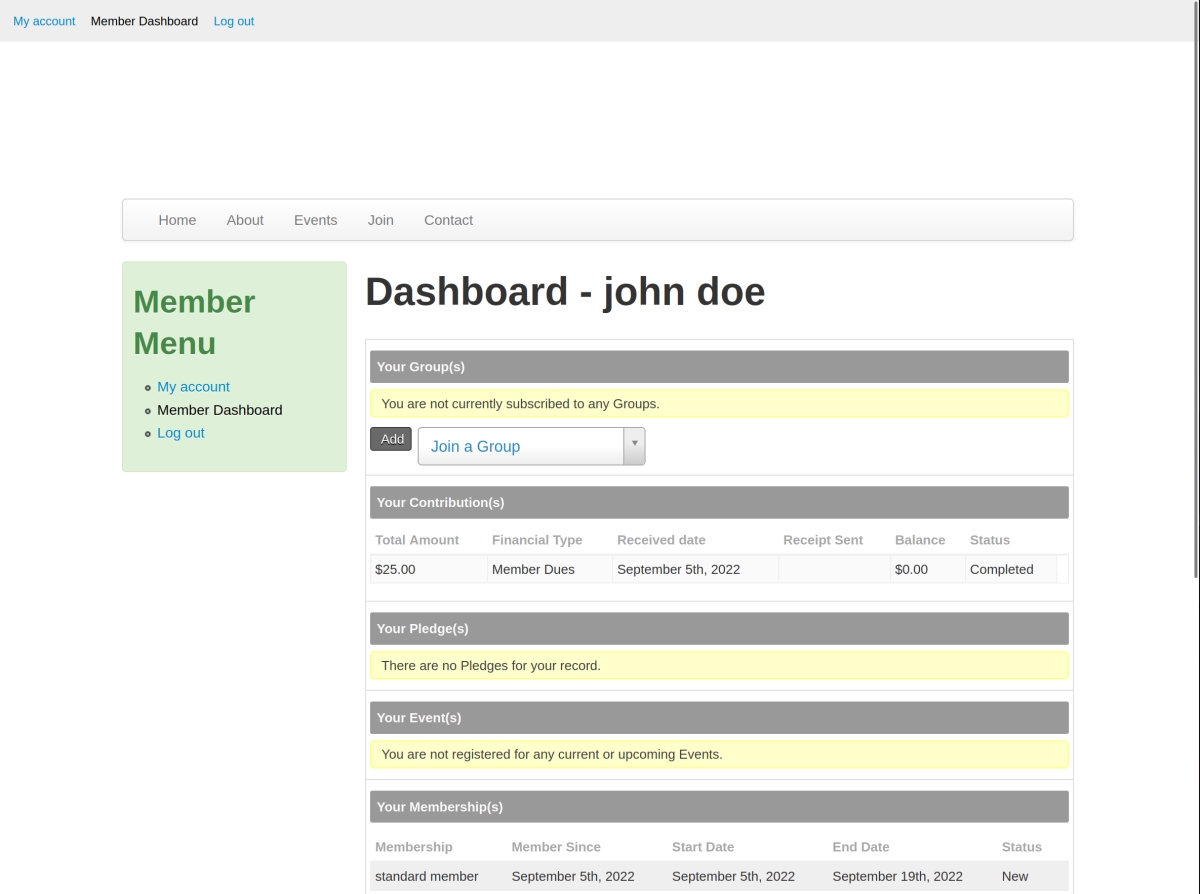
CiviCRM is a perfect fit for any organization that collects membership dues, such as a chamber of commerce.
Free consultation?
Book now. No commitment.
hello@covingtoncreations.com
will reply in 24 hrs
570.508.6881 (or SMS)
9-5 mon-fri
Design & Development
Wordpress, Drupal, Joomla
New custom websites, bespoke themes and extensions, redesigns, upgrades, migrations
Optimization & SEO
Let us optimize and manage your overall online presence. We offer full service monthly SEO as well as one-time projects.
Maintenance, Patching
White glove monthly backups, security updates, maintenance and testing for your Wordpress, Drupal, or Joomla site.